Today’s CIOs are not only fighting a war against cyber threats, they are also fighting a war internally against efficiency, proficiency, and visibility.
Best of Breed Mindset
There has always been a “best of breed” technology mindset within IT. Best of breed defines an approach of leveraging a platform or solution that is best suited for each desire task. This tended to lend itself to having many vendors and technologies to manage. Most of this was done for client-facing needs: the best platform for Identity Management, the best platform for Printer Management, the best platform to provide IT with metrics and reporting around a specific need, etc. Many times, the definition of “best” was the ability to assimilate the solution into the daily lives of users and the ease of use from an IT management perspective. And, yes, of course the best of breed platform had to work.
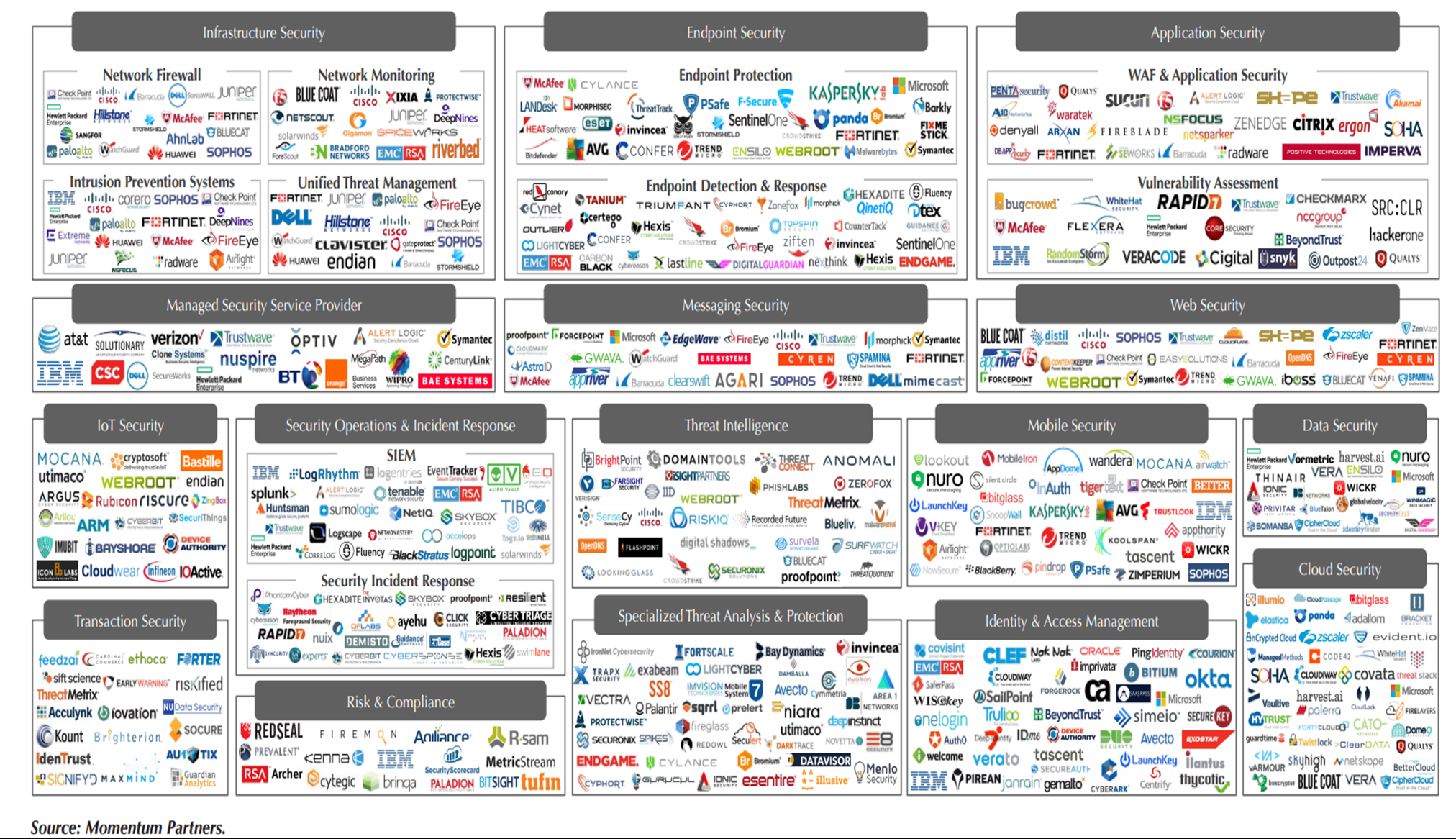
I believe today’s selection strategy has evolved. I believe the catalyst for this evolution is cyber security. Why security? Well, take a look at the graphic (security placemat); this graphic represents some of the vendors considered “best of breed” in various cyber security focus areas. Now, imagine you’re a security professional working for an organization who invested heavily in cyber security technologies that covered the focus areas in the graphic. Each area could (and most likely would) have differing platforms. Where do you start? What do you look at first? Are these systems talking to one another? If they are talking to one another, are they taking into consideration each other’s findings before measuring risk? Do they play nice together?
The answer to that conundrum has always been to use yet another platform, a SIEM tool. SIEM tools monitor and manage all those disparate systems. Wait a minute! We just invited yet another platform to our head-spinning cyber security party!
In the last few years, major players, yes, even best of breed players too, have seen this trend developing. Their response has been to either develop or acquire complimentary technologies to develop a platform that can be multi-faceted and tasked to address the many areas of security focus identified on our graphic.
So what does all this mean?
Well, with the recent evolution of the best of platform concept, I believe today’s CIOs need to take this into consideration when going through a cyber risk and software selection process. Perhaps take a moment to think about breaking away from the best of breed concept and take a hard look at best of platform. Put the major best of platform players through the evaluation process. I believe the results may surprise you.
As I’ve gone through this process, here are my high-level pros and cons:
Best of Platform Pros
- Single Point of Management – One Interface to Manage
- Ease of Adoption and Training
- Improved Process/Procedure Development
- Improved Reporting and Visibility
- Ease of Vendor Management (one vendor, not many)
Best of Platform Cons
- Many Points of Management – Many Interfaces to Manage
- Potential to Include Unnecessary and/or Unwanted Features or Capabilities
- Increased Learning Curve
In contrast, when we look at best of breed technologies, I’ve found:
Best of Breed Pros
- Specific or Targeted Solutions
- Open Integration Often Included (not always, but likelihood is higher in this segment)
Best of Breed Cons
- Disparate Systems, Management Points, and Views
- Requires Multiple Vendors, Implementations, Contracts, etc.
- Higher Potential for Conflict or Incompatibility with Systems, Data, and/or Infrastructure
- Must Learn and Implement Multiple Platforms
Remember, my pros and cons are provided here at a high level and are certainly not complete. You will need to review your options and select what is best for you. Not all organizations may warrant the best of platform concept, but I believe organizations and their leadership should take a harder look at these options.
All of the analysis starts with an organization’s needs. But with that mind, needs change, as does the technology options available, so the needs and options of yesterday may not work tomorrow. Yes, this can get quite complex very quickly. But with your unique needs in mind, you will find options available to you to help you protect your organization’s digital estate.
To learn more about platform security solutions, or to receive more information about our services, contact us.

